Use Case 2 · Home Monitoring Security System for Ageing People (Santander, Spain)
Overall description
Worldline proposes Senior Care for Use Case 2, an IoT platform that allows tele-assistance companies to digitalize their current services by using an innovative and secure platform to monitor the well-being of ageing network tele-assistance users, guaranteeing security and integrity of all the activity data collected from the home sensors deployed in an end to end approach thanks to the M-Sec components developed for the purpose.
Based on the data collected from sensors such as bed occupancy sensor, door/window opening sensor, movement sensor,.. and by having previous configuration of certain rules to detect emergency situations or unusual users’ behavior, tele-assistance companies can act and provide immediate response in case of alerts and/or emergency.
Challenges it addresses
The rapid increase in the population in recent years, caused by the increase in life expectancy due to medical, social and economic advances, the lack of close family ties, the result of living alone, together with the increase in the demand for social services and the risks generated by the Covid-19 crisis, make it necessary to rethink innovative well-being solutions and services, as well as find complementary or alternative models to the current ones. In order to guarantee the safety and tranquility of people who may be at risk due to factors of age, frailty, loneliness or dependency, Worldline proposes Senior Care.
Another current challenge faced in today’s IoT Applications has to do with the security and integrity of the data collected, the main problem for its applicability and scalability. In the case of a solution like Senior Care, the sensors deployed continuously collect personal information that a malicious actor can use to track down and commit malicious actions. However, thanks to M-Sec, it is possible to go beyond GDPR compliance by adding additional security mechanisms that prevent external attacks that can lead to erroneous actions by tele-assistance companies.
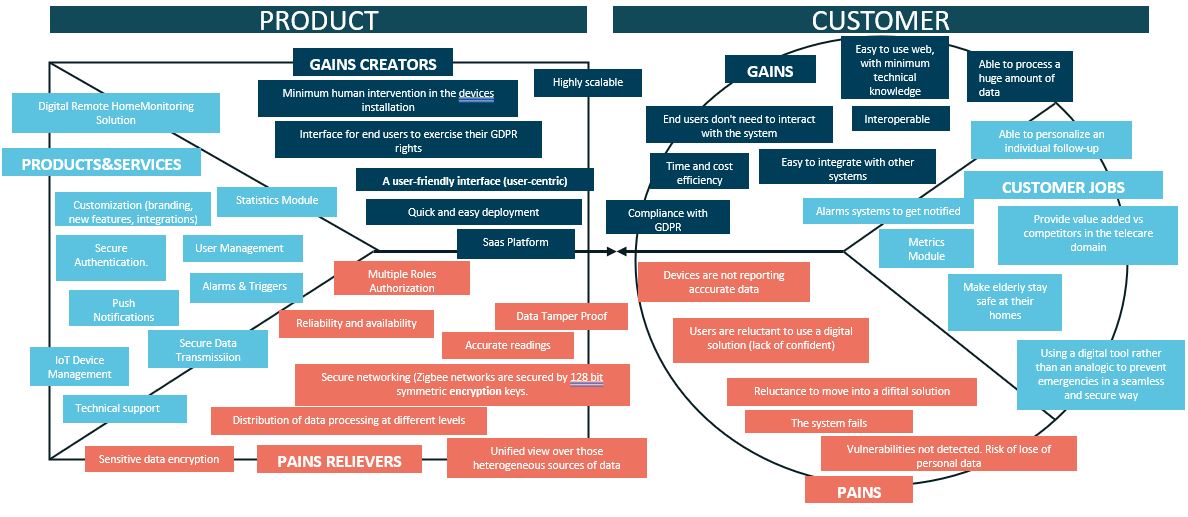
(left click the picture for a better view)
The M-Sec approach
Thanks to M-Sec, the collection and transfer of data is carried out in an interoperable and scalable way thanks to the use of protocols through which data can be received from different sensors and from different manufacturers. Including an access control mechanism that allows only authorized people to read raw data or interact with IoT devices.
Regarding the storage layer, the consortium uses blockchain technology. Blockchain is a chain of blocks (decentralized database) where all data is linked, encrypted and distributed, allowing transactions to be carried out safely without the need for intermediaries. All the information registered in the blockchain cannot be erased or modified. Thanks to the immutability feature, it is possible to transform the audit process into a fast and efficient procedure. Suppose we want to add a layer of security to the traditional encrypted data storage system that takes place offchain (outside the blockchain). In this scenario, M-Sec allows generating a hash that is simply an alphanumeric code generated from a text string and automatically saving it as an on-chain transaction (in the blockchain itself), allowing you to verify at any time if the data has been modified since any attempt to manipulate the data would change the resulting hash.
In addition and at the application level, M-Sec mechanisms to comply with low development effort with the rights of data subjects which includes functionalities mainly for the right of access, the right to rectification, the right to erasure, the right to restrict processing, the right to data portability, among others.
Finally, anonymised data (mainly raw activity data from sensors), is transferred to the M-Sec marketplace where stakeholders who may be interested on getting home activity data can buy the data using M-Sec Tokens, which is a cryptocurrency in the form of a smart contract running in on blockchain. The deployed smart contracts communicate with each other to verify the sufficient funds of the buyer and complete the purchase by transferring funds from the balance of the buyer to the one of the data owner.
Pilot implementation
The pilot targets a total number of five participants from Atenzia user’s network (tele-assistance company piloting the solution with more than 25 years providing prevention and care services to the elderly). A Home Sensor Kit was distributed to each participant including a gateway, bed occupancy sensor, movement sensor, door/window open sensor and a smart plug. Pilot initiated last September 2020 and will finalize in August/September 2021. During these months, Worldline with the Support of Santander Municipality and Atenzia, has been evaluating functional and non-functional requirements implemented frame in order to validate the secure infrastructure provided by M-Sec.
(left click the picture for a better view)
Main results and next steps
The main results from the pilot conducted are listed below:
Atenzia, as the teleassistance company piloting UC2, is quite satisfied with the ease of use and the Look and Feel of the solution provided, as well as the ease of installation of the home sensors at the user’s home. They are satisfied in the way Senior Care has helped them to solve their problems, feeling safe using Senior Care as their current system. They are satisfied with the reliability of the information provided by the Senior Care system, as well as how this system and the M-Sec Project can help to reduce the breach about current security concerns in terms of data protection and increase user trust.
Regarding pilot end participants, they reported feeling safer with the new sensors installed in their home while one of them reported feeling the same degree of security with and without the new sensors. In terms of Privacy, all of them agreed that none of them have felt their intimacy invaded at any time. Furthermore, sensors installation have not caused them inconvenience at any time.
Lessons Learnt
Regarding lessons learnt, two aspects did not work as expected:
- Bed occupancy sensors were not working properly. The main problem was the connection between bed mattress and sensor. It has been addressed with the supplier of the devices.
- The integrated prototype with M-Sec components. After performing all integrations with sensiNact, Security Manager, Marketplace, and the Blockchain Middleware and testing them on a development environment, the standard procedure to promote the software to a production environment was performed. Once the software was on production we faced some problems and new challenges. One of the problems was to overcome the downtimes in the Blockchain Middleware and the Marketplace, due to the huge fires in Greece, by creating some new software, as quick as possible, called bridge in order to let the system work properly even without communication. These new bridge were a challenging task because of the importance and the time we had. Another problem was due to the stress testing performed in the Security Manager system that make the servers unstable some days and let us with a communication problem. The Crypto Companion DataBase is secured by the Security Manager, and could not be accessed in a proper and stable way to save and retrieve data. After analysing this situation we could not find a proper way to solve this downtime, as the security was entirely delegated to the Security Manager.
In addition, even though an export method was implemented to analyse data collected from sensors, Atenzia required to have a new feature to export the data in an aggregated way from all users registered in the platform. This will help in the preparation of a report to be submitted to the municipal Social Services service on the results of the pilot.
Overall, Atenzia staff who have participated during the Senior Care pilot phase trial feel quite satisfied with the ease of use of the tool and the look & feel of the solution provided. They also highlight the ease of detecting unusual behaviours of end users through the alert system implemented. One of the key aspects is that thanks to M-Sec, it has been possible to bridge the gap on current security concerns in terms of data protection and increase user confidence. Finally, in terms of home sensors, they highlighted the ease of their installation.
With regard to end users, those who have had several home sensors installed in their homes, in terms of security, all participants reported feeling safer with the new sensors installed in their home. In terms of privacy, all agreed that none of them had their privacy invaded at any time.
How can I join?
Contact Vanessa Clemente Nunez: vanessa.clementenunez@worldline.com