On the 9th of March, M-Sec hosted an EU Industry Week 2021 local online event, presenting its secured framework for smart cities and the main project achievements. Take a sneak peek at what was discussed
On the 9th of March, at 10am CET (Brussels Time), M-Sec presented a local online event in the scope of EU’s flagship initiative EU Industry Week 2021, entitled “Developing a secured IoT smart city framework for a better digital futureâ€, with the main goal of discussing the challenges related with security and privacy in smart cities and how the M-Sec framework could help overcome them, and thus support the shaping of Europe’s digital future.
The Webinar started with a presentation of the M-Sec Survey, by Nadine Teles, EU Projects Manager at F6S Network Limited. With more than 250 answers, this online survey to all EU and Japanese IoT citizens and stakeholders, considered as potential users of the M-Sec solution, aims to collect feedback on their experience when using IoT devices and applications and on their knowledge of EU and Japan’s data protection regulations. The main goal of this survey is to help the project better understand the IoT ecosystem in which M-Sec is expected to operate, what are people’s main IoT habits and their awareness regarding data protection regulation in their region.
From an initial sample of 250 answers, most respondents (56%) identified health devices – such as fitness bracelets – as the IoT device that they most commonly use, followed by smart watches, home devices and appliances and voice assistants. 36% of respondents seem to use those devices every day, all day, which shows how they are becoming part of citizens daily lives and routines. However, most of them (53%) are not fully aware of security and privacy data protection policies of the IoT devices and applications they use, meaning that they do not always carefully read those policies when start using a device of application or when those policies are updated by the provider. Therefore, when confronted with a hypothetical scenario in which a given IoT device or application suffers a cyber-attack, respondents prefer to stop using that device or application immediately and go through the data protection policies to become more aware of their rights. Main privacy and security concerns seem to be more related with the wrongful use of data by others (>60%) than the actual malfunction of the IoT device or application itself. Regarding EU and Japan’s GDPR and APPI data protection regulations, EU respondents show a satisfactory level of awareness (>80% are fully aware or have heard about it), while most Japanese respondents are not acquainted with their data protection rights.
The preliminary results of the M-Sec Survey were followed by a short live consultation to all participants, that showed the same trends as presented above.
Next, Vanessa Clemente, Business Developer & Project Manager at Worldline Spain, and M-Sec Project Coordinator from the EU side, explained the main purpose of M-Sec and what problem is it is trying to solve. In a world with increased access to the Internet and a rise in the number of IoT devices and applications used, there is also a need for an increased concern regarding privacy and data protection of the flows of data exchanged between those devices due to an increase in the number of cyber-attacks over the last years, namely in hyper-connected smart cities. The main objective sought by M-Sec is, thus, to develop a framework that provides security and integrity of data traffic, end to end, from the device to the cloud and to the application in a secure and transparent way.
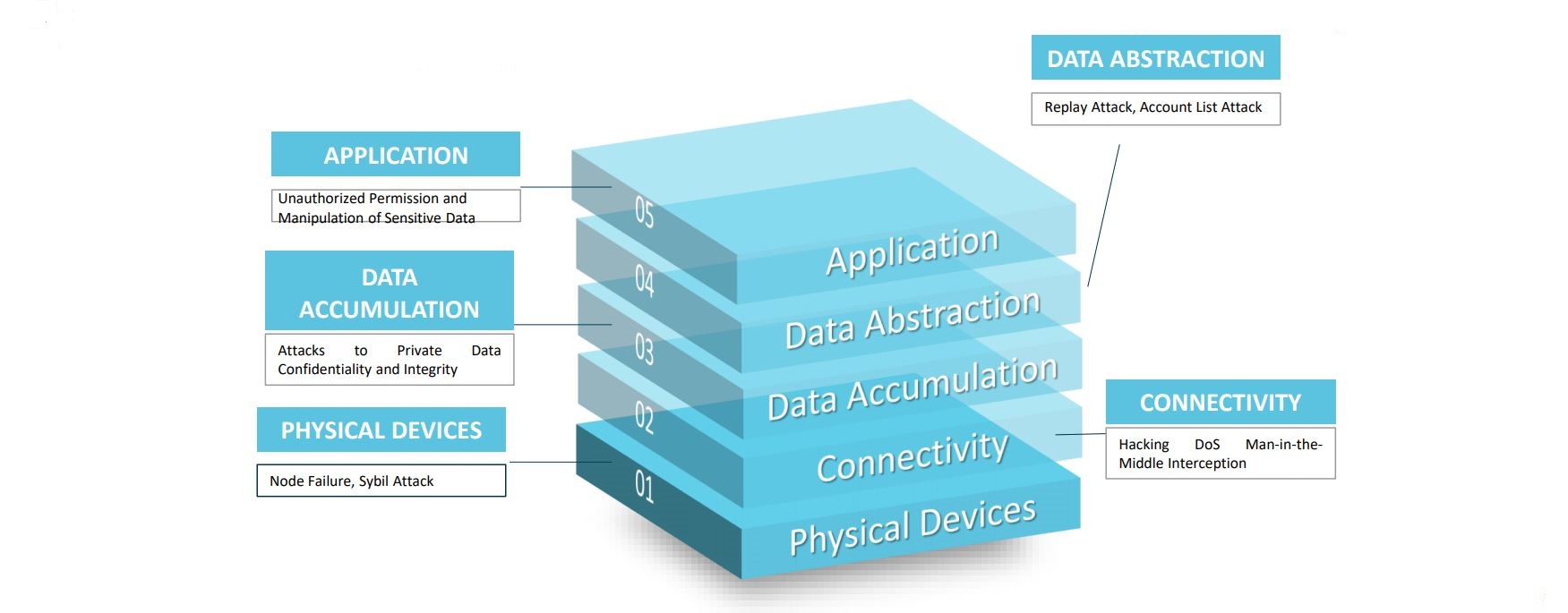
Picture 1: examples of (cyber)attacks to IoT devices and applications
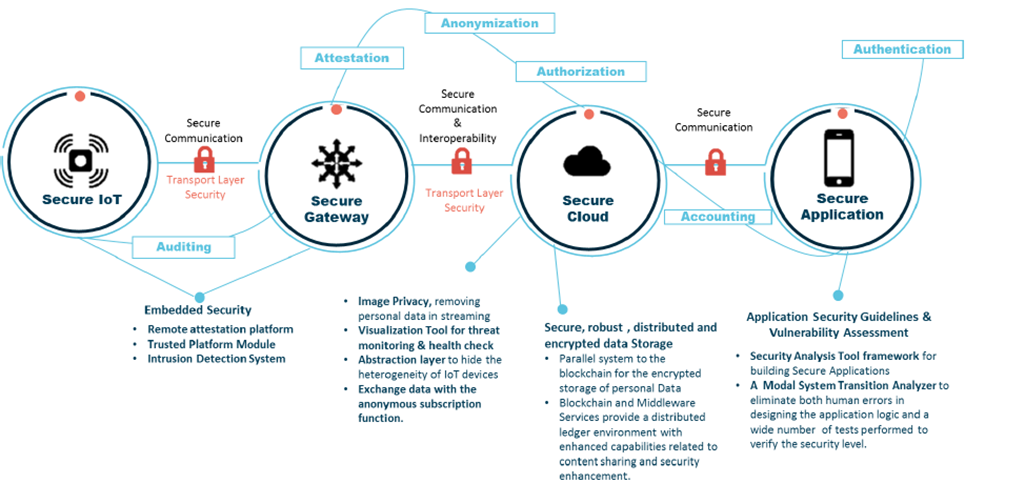
Afterwards, Antonis Litke, Senior Research Engineer at the Institute of Communications and Computers Systems (ICCS) of the National Technical University of Athens, gave a more technical explanation about the M-Sec framework, how the project and the corresponding solution has progressed, the work that still needs to be done, and also expected achievements. After a brief presentation of the overall M-Sec architecture and all the security layers that this solution was trying to tackle – IoT devices, Cloud, Marketplace and applications for the end-users -, the speaker focused on the middleware layer of this technology and explained how the M-Sec researchers are trying to connect IoT devices (i.e., data providers) and applications (i.e., data consumers) in a secure way, by implementing the basis blocks for connectivity, service abstraction, device management, virtualization, and remote access.
Aamir Bokhari, Information Security Officer at Yokohama National University, in Japan, then highlighted the data security and privacy approach behind the M-Sec solution, namely by explaining why smart cities need confidentiality, integrity, availability and privacy of the IoT data exchanged due to the increased use of IoT devices and applications, and how the secure use of the data collected by those devices can improve public policy and, ultimately, citizens living experience in a given municipality. Therefore, the goal of M-Sec consisted of looking for techniques, methods, design and operating principles that minimized the risk of this multi-layered security solution to suffer critical vulnerabilities, which could be leveraged by hackers to carry out a number of nefarious activities, and at the same time protect the privacy of the data exchanged by users of IoT devices and applications.
Picture 2: different levels of security considered in the M-Sec solution, end to end security
Finally, Vanessa Clemente closed the session with a brief insight into each use case that M-Sec is implementing in order to test and validate the main principles behind the M-Sec multi-layered solution. The 5 use cases are spread over two cities: Santander, in Spain, and Fujisawa, in Japan. Each Use case aims to facilitate a specific area of a smart city life, from improving the wellbeing of the growing elderly population, to monitoring rubbish collection, to creating playable city games, with the M-Sec innovation of security and privacy of all the data that is exchanged between users in each use case.
Whether you did not have the chance to attend the event or you enjoyed it so much that you want to go for it a second time, here is the recording of the event: