About
A EU-Japan collaboration which stands for “Multi-layered Security technologies to ensure hyperconnected smart cities with Blockchain, Big Data, Cloud and IoTâ€.
The main goal of M-Sec project is to research, develop, deploy and demonstrate multi-layered Security technologies to ensure hyper connected smart cities and empower IoT stakeholders with an innovative platform which leverages blockchain, BigData, Cloud and IoT security, upon which they can build innovative smart city applications.
WHAT DOES
M-SEC DO?
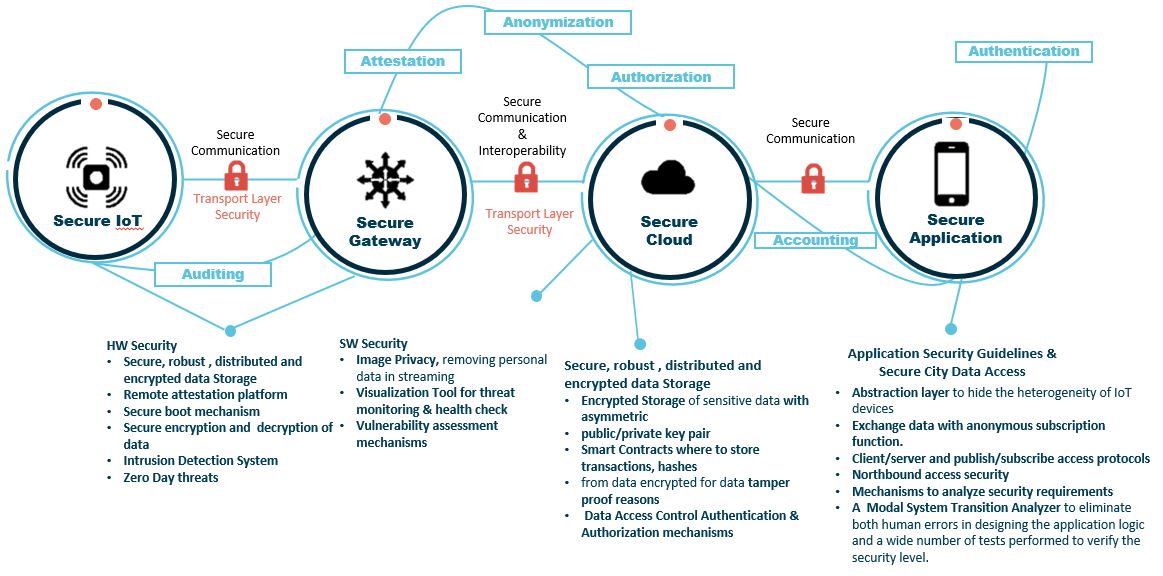
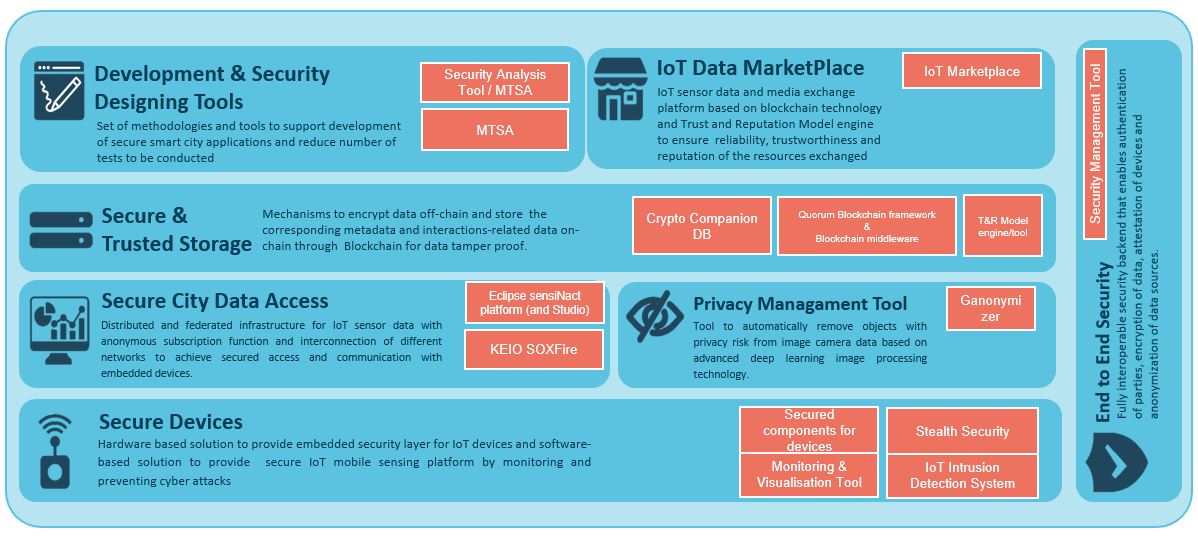
The project explores secure, interoperable interactions between IoT elements based on a holistic secured cloud/edge/IoT context within a future smart city. Overall, the M-Sec paradigm complements mainstream IoT/cloud technologies, through enabling the introduction and implementation of specific classes of applications and services, which are not efficiently supported by state-of-the-art architectures.
M-Sec Results
M-Sec ended on September 2021. Here are the 4 main results:
The M-Sec smart city platforms will be distributed and robust, and based on IoT, cloud, Big Data and blockchain technologies. Through this trusted infrastructure, IoT stakeholders will be empowered to develop and operate new IoT applications for smart cities on top of smart objects. Follow our pilots in real-life smart cities: Santander (Spain) and Fujisawa (Japan)!
Build and experiment with new ideas and application services for smart cities! Startups, SMEs and developers will be connected to the M-Sec actors and be given access to a complete set of tools and infrastructures.
Our open market of applications, data and services will facilitate the exchange of value and information between IoT devices and people through virtual currencies. Check the incentives that motivate the interaction between smart objects and humans.
Learn how to replicate the M-Sec approach in your city! Our revenue model will guarantee the return on investment and all M-Sec benefits.
Interested in knowing more?
Sign up to the M-Sec newsletter and/or join our Slack Community and stay up to date with our events, news, and developments.
M-Sec Factsheet
- Project title: Multi-layered Security technologies to ensure hyper connected smart cities with Blockchain, BigData, Cloud and IoT
- Project Acronym: M-Sec
- Grant Agreement Number : 814917
- Type of action : RIA Research and Innovation action
- Topic: EUJ-01-2018 Advanced technologies (Security/Cloud/IoT/BigData) for a hyper-connected society in the context of Smart City
- Starting date: 01/07/2018
- Duration: 36 months
- Keywords: Security, IoT, Cloud, Smart Cities, Blockchain
- Coordination EU: Worldline Iberia SA (Spain) – Contact: Vanessa Clemente ([email protected])
- Coordination JP: NTT East (Japan) – Contact: BBX Marketing Department ([email protected])

